What are the Key Updates in ISO 27001:2022?
The main differences between ISO 27001:2013 and its 2022 version are as follows:
Mandatory clauses – ISO 27001:2022 introduces new requirements for understanding the needs of interested parties, identifying necessary processes and their interactions, and planning changes within the ISMS.
Annex A – The revision of Annex A in ISO 27001:2022 includes 93 controls grouped into organizational, people, physical, and technological controls.
ISO 27002:2022 impact – Changes in ISO 27002:2022 have influenced ISO 27001:2022, particularly in clauses 4 to 10, with minor updates and terminology changes. Particularly in these clauses:
Clause 4.2 Understanding the needs and expectations of interested parties
Clause 4.4 Information Security Management System
Clause 6.2 Information security objectives and plans to achieve them
Clause 6.3 Planning of changes
Clause 8.1 Operational planning and control
Clause 9.3 Management review
Clause 10 Improvement
Transition – Existing ISO/IEC 27001 certificates are not affected by the changes in ISO 27001:2022. However, individuals seeking certification against the new version should consider the updated training courses available.
Preparing for ISO 27001 Certification in 7 Steps
It takes a lot of time and effort to properly implement an effective ISMS and more so to get it ISO 27001-certified. Here are some steps to take for implementing an ISMS that is ready for certification:
Review processes and ISO 27001 – Familiarize staff with the international standard for ISMS and know how your organization currently manages information security and information systems.
Get employee buy-in – Help employees understand the importance of ISMS and get their commitment to help improve the system.
Conduct risk assessments – Determine the vulnerabilities and threats to your organization’s information security system and assets by conducting regular information security risk assessments and using an iso 27001 risk assessment template.
Implement controls – Information or network security risks discovered during risk assessments can lead to costly incidents if not addressed promptly.
Conduct gap analysis – Use an ISO 27001 audit checklist to assess updated business processes and new controls implemented to determine other gaps that require corrective action.
Do internal audits and employee training – Regular internal ISO 27001 audits can help proactively catch non-compliance and aid in continuously improving information security management. Information gathered from internal audits can be used for employee training and for reinforcing best practices.
Contact your auditor for certification – Prepare your ISMS documentation and contact a reliable third-party auditor to get certified for ISO 27001.
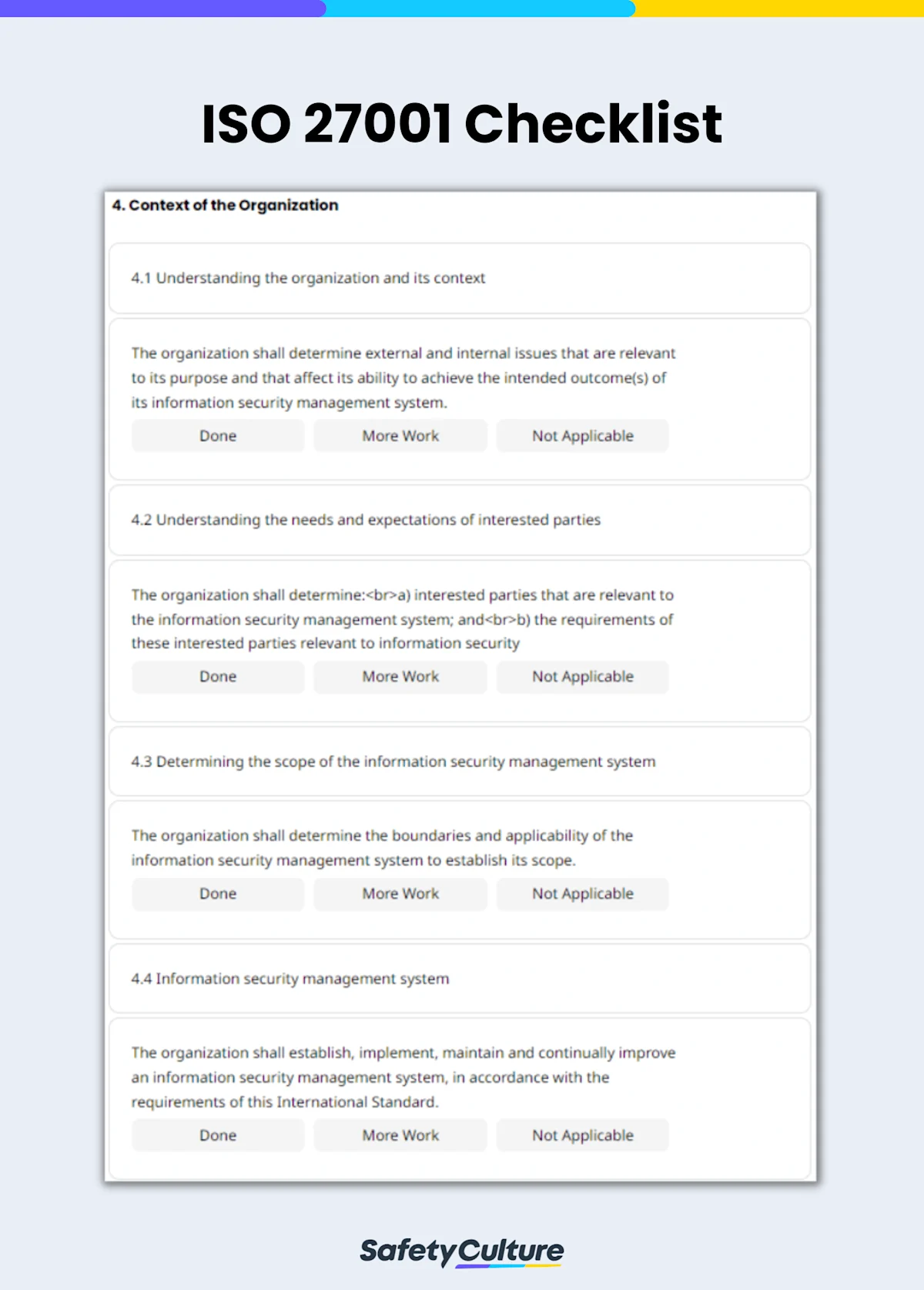
What is an ISO 27001 Checklist?
An ISO 27001 checklist is used by Information security officers to correct gaps in their organization’s ISMS and evaluate their readiness for ISO 27001 certification audits. An ISO 27001 checklist helps identify the requirements of the international standard for implementing an effective Information Security Management System (ISMS).
Assuming that the organization has implemented the necessary changes to meet the standard security requirements of ISO 27001, a checklist will help in raising security awareness and in identifying gaps in the organization. Below are steps you can take to effectively evaluate your organization’s readiness for certification:
How to use an ISO 27001 Checklist
Determine if the organization understands the context of the information security management system.
Verify if there is adequate leadership and policies in place to demonstrate the organization’s commitment.
Check if the organization has a system in place to identify and understand risks.
Gauge if the competency of employees, resources available, awareness, and communication are suitable.
Determine if the organization plans, implements, and controls processes in a manner that meets the ISMS requirements.
Confirm if the organization has a system in place to monitor, measure, analyze, and evaluate the ISMS.
Verify if nonconformities are addressed with corrective actions.
Provide comments and recommendations.
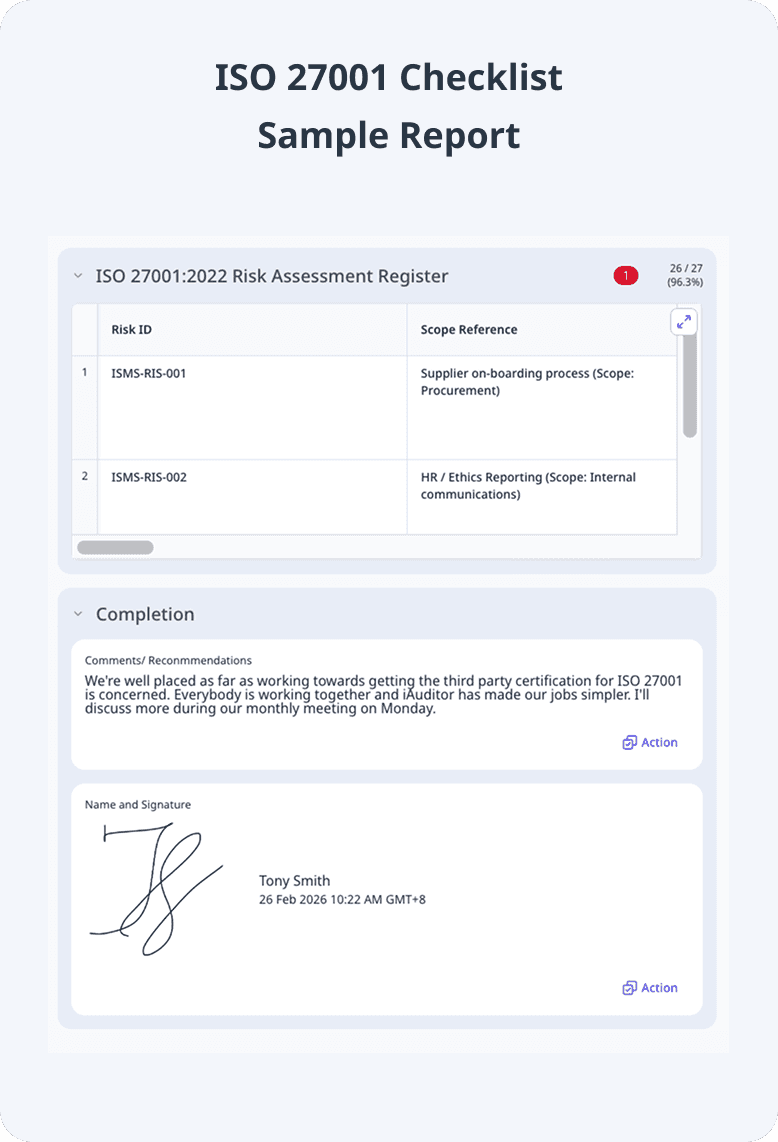
Use a table format for the risk assessment register to improve reporting accuracy.
Sign off with name and signature as completion of the audit.
Share with key stakeholders and use the information gathered from the audit.
Preview ISO 27001 PDF Report