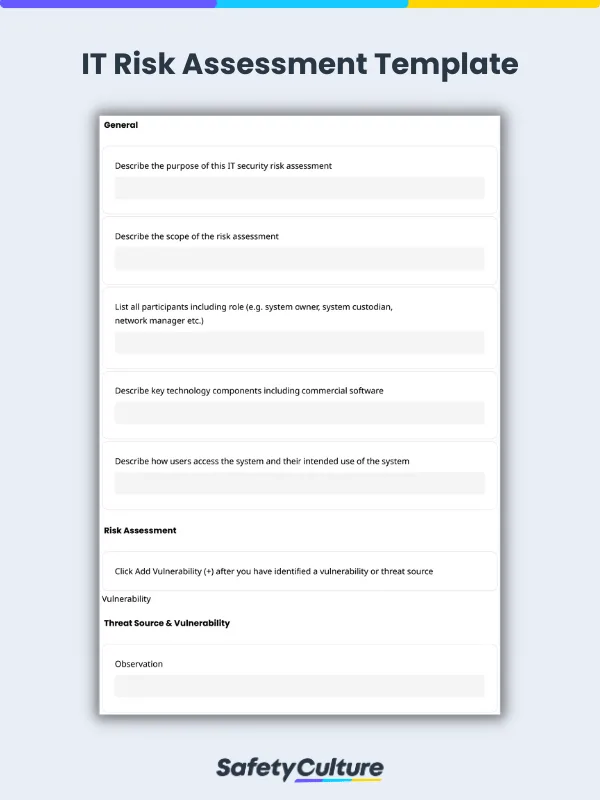
What is an IT Risk Assessment Template?
An IT risk assessment template is a tool used by information technology personnel to anticipate potential cybersecurity issues and mitigate risks to organizational operations.
IT Risk Assessment Checklist Steps
Steps to consider when conducting an information security risk assessment:
Identify the purpose of the risk assessment
Consider key technology components
Identify and observe the vulnerability or threat source
Evaluate the risks
Recommend controls or alternative options for reducing risk
Vulnerabilities and Threats to Information Security
Be mindful of these latest threats and vulnerabilities that your company may need to proactively deal with:
Ransomware
This is a malware designed to illegally access personal data and restrict victims’ access to their proprietary information while forcing them to pay a ransom. Large companies have fallen victim to ransomware attacks costing hundreds of millions of dollars.
Major data breaches
Data breaches happen because of various reasons such as weak or stolen credentials, compromised assets, or card frauds, among others. Cyber attacks such as this threaten to expose massive data on customer and company information.
Malware and malicious mobile apps
This type of vulnerability is normally caused by applications gotten from untrustworthy or malicious sources. The tactic is to gather personal information and other data without the user’s permission and knowledge—which can then be used in various negative ways.
Computer hijacking
Also called cyber hijacking, computer hijacking is the processing power of company computers hijacked for cryptocurrency mining. It is a type of information threat where an attacker can take control of the network of computers and software programs used by an organization.
Artificial intelligence
Attackers also administer the use of machine learning to build better hacking programs and implement more targeted phishing techniques. With the use of artificial intelligence, they keep track of potential victims’ online patterns, defenses, and vulnerabilities.
Internet of Things (IoT)
Along with the progress of technology comes a considerable increase in threats to information and an even more threat to private data. More connected devices mean greater risk, making IoT networks more vulnerable to overload, lockdown, or getting compromised.
Vulnerabilities and threats to information security can be found and addressed by conducting IT risk assessments.
7 Key Items for Information Technology Risk Assessments
Consider these key points when conducting IT risk assessments:
1. Identify company assets
These could be proprietary information, hardware, software, client information, network topology, etc. It’s best to collaborate with other departments to determine other valuable company assets and which ones to prioritize.
2. Recognize the threats
Be aware of these main sources of threats that an organization usually encounters:
Natural disasters
Human error/malicious intent
System failure
3. Spot the vulnerabilities
Vulnerabilities are security weaknesses that can expose information, data, and assets to various threats. Conduct internal audits, penetration testing, continuous employee training, and raise awareness to find IT vulnerabilities in your organization.
4. Assess the likelihood of incidents
Evaluate the assets’ vulnerability to threats, from there, assess the likelihood of an incident happening. This can be done while considering various factors that affect an organization’s security such as risks, compliance and policy, and continuity plans, among others.
5. Specify possible repercussions
One or a combination of the following can happen if company assets get impacted by threats and other forms of vulnerabilities: legal action, data loss, production downtime, fines and penalties, negative impact on company reputation, etc.
6. Determine controls
Determine what controls are already existing to mitigate threats. From there, work on identifying how to improve governance and protection against potential vulnerabilities. New controls may need to be implemented or old ones updated to adapt to new and changing threats.
7. Improve continuously
Conduct risk assessment regularly or as frequently ideal as possible. This helps proactively identify inconsistencies in security, thus, addressing them even before they cause actual threats. Document and review the results of IT risk assessments and always watch out for new security issues.
IT Risk Assessment Example
Describe key technology components including commercial software:
Door magnetic lock, laptops, headsets, company proprietary software. Describe how users access the system and their intended use of the system:
Only admins have access to the site and they can only use the company-issued laptops with the installed company software intended for attendance logs. Observation:
Employee’s new laptop was not password protected. Anyone curious or intending to access information on that laptop within the premises can access it. Threat source / vulnerability: Intentional insider Existing controls:
All laptops have designated users who are responsible for the security of the data and device. All laptops are kept in designated lockers after the day. Door has a magnetic lock that can be opened by the proximity card of employees. Consequence: Medium Likelihood: Unlikely Risk rating: Low Recommended controls:Employee needs to create a strong password to protect his laptop from unintended use.