Powered by
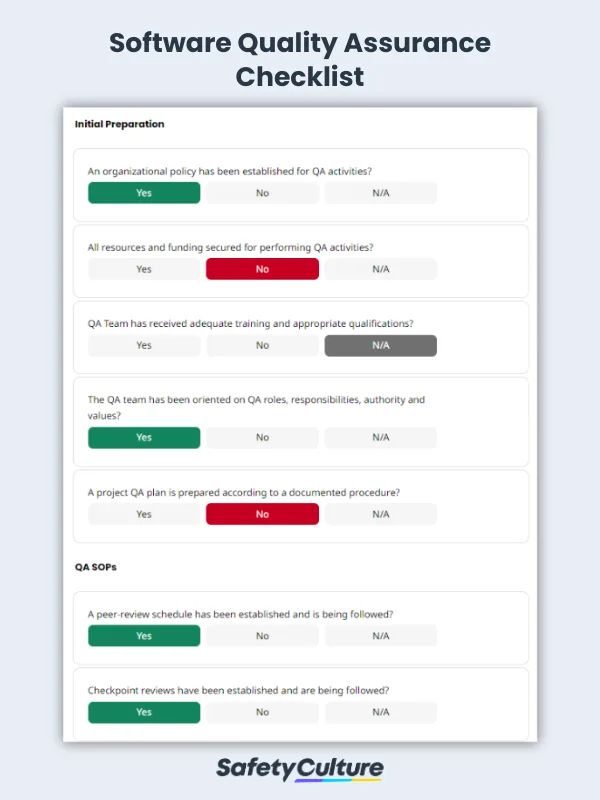
Software Quality Assurance Checklist
Improve and maintain software quality by using a digital SQA checklist
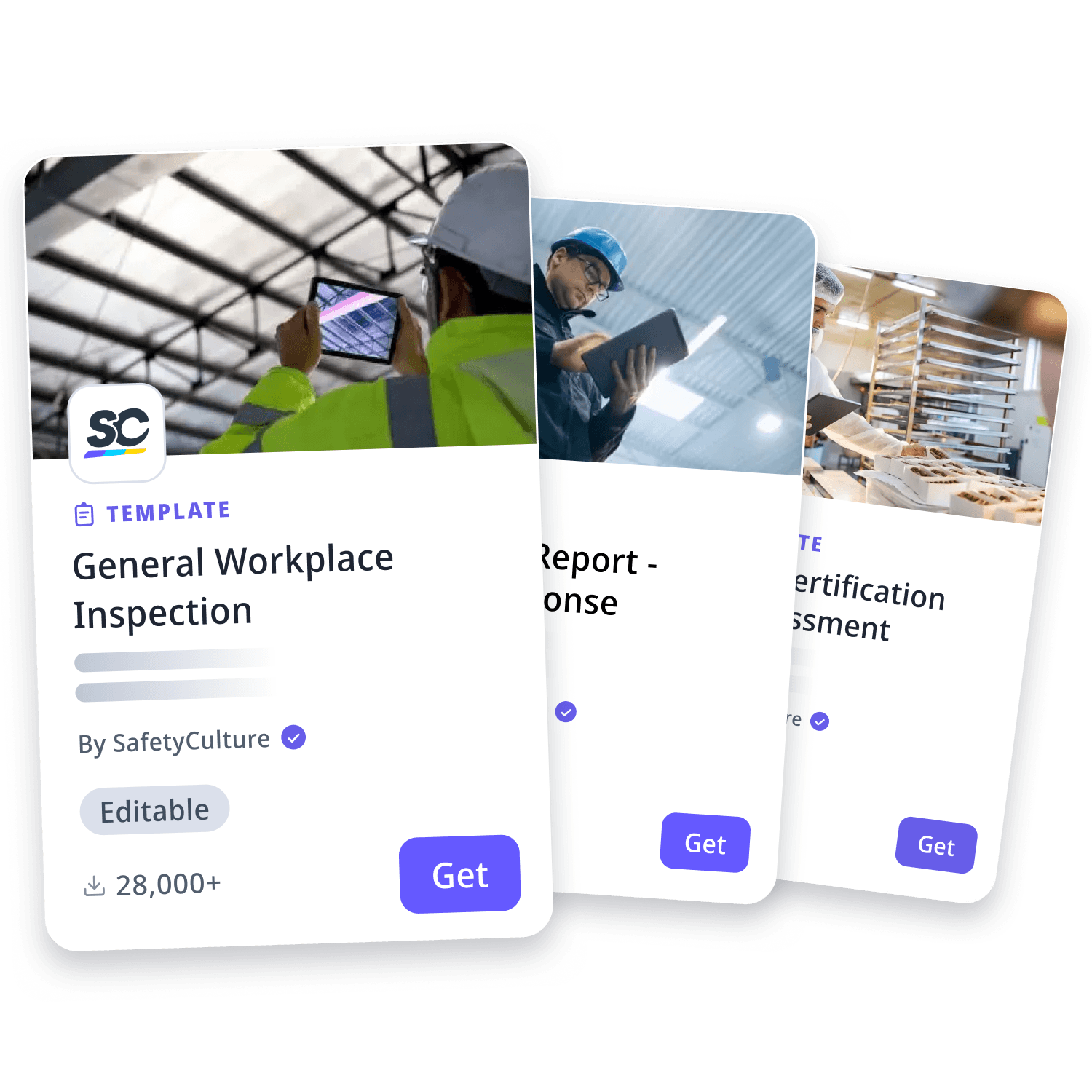
Why SafetyCulture digital checklists?
Free to use for up to 10 users
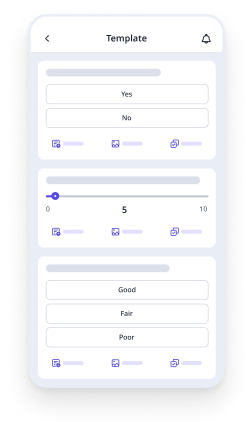
Eliminate paperwork with digital checklists
Generate reports from completed checklists