Who needs to be DFARS compliant?
Contractors and subcontractors of the Department of Defense must follow the standards set by the NIST in SP 800-171 to be considered DFARS compliant.Failure to comply with DFARS, also known as the cyber DFARS clause 252.204-7012, can result in suspension, financial penalties, termination of contract, or even debarment from working with the Department of Defense.
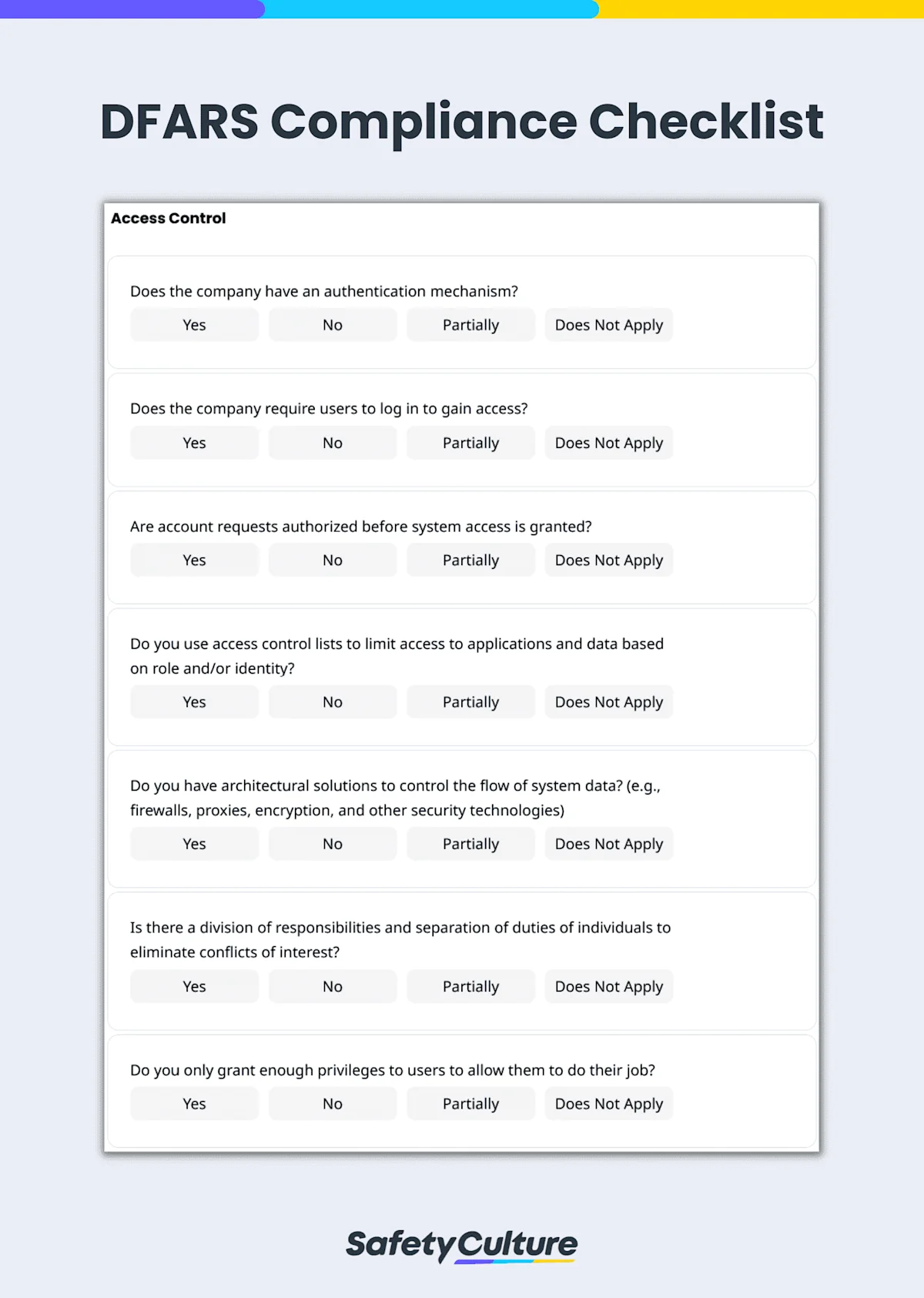
What is a DFARS Compliance Checklist?
A DFARS compliance checklist is a tool used in performing self-assessments to evaluate if a company with a DoD contract is implementing security standards from NIST SP 800-171 as part of the process for ensuring compliance with DFARS clause 252.204-7012, “Safeguarding Covered Defense Information and Cyber Incident Reporting.”
Maintain DFARS Compliance with Self-Assessment Checklists
A DFARS compliance self-assessment checklist is a tool used by manufacturers or contractors to evaluate current mechanisms in place to ensure adequate security for information systems. Self-assessment checklists can also serve as a guide for DoD contractors in complying with DFARS rules and regulations.
How to Use the DFARS Compliance Checklist
Since the primary purpose of DFARS documents is to ensure that DoD contractors and subcontractors are complying with their set requirements, it is ideal to conduct self-assessments using a digital checklist. DFARS checklist enables users to dive deeper into how organizations can maintain compliance and protect their confidentiality to avoid a data breach and other significant consequences.
Steps to Using the DFARS Compliance Checklist
For an efficient and effective tracking of DFARS compliance, follow these steps:
Ask the right questions – Review your checklist to ensure that it corresponds to the DFARS requirements for compliance. Some of the areas to include are access control, training and awareness, audit and accountability, configuration management, and identification and authentication, among others.
Check each item in detail – As you go through each area of the checklist, inspect all items comprehensively. This helps prevent missing critical items that could negatively impact the organization’s general cybersecurity health or ultimately lead to DFARS non-compliance.
Assess compliance level – Evaluate compliance in a detailed manner by specifying if an item complies, doesn’t comply, or impartially complies according to the required level from DoD. This enables you to quickly identify areas that need to be improved or worked on.
Attach media evidence as needed – Strengthen self-assessment documentation by adding a photo or video evidence of non-compliance for easy identification and reference.
Complete with relevant signatures – Finalize the checklist by attaching signatures of the assigned IT specialist and contractor, then generate a report to be shared with relevant stakeholders.
A Guide to DFARS Compliance Requirements
Below are sample questions you can use for your DFARS compliance self-assessment checklist. These questions are derived from the “Self-Assessment Handbook NIST– Handbook 162” provided by the NIST:
Access Control
Does the company have an authentication mechanism?
Does the company use access control lists to limit access to applications and data based on role and/or identity?
Do you only grant enough privileges to users to allow them to do their job?
DFARS Training and Awareness
Do all users, managers, and system administrators receive initial and annual training commensurate with their roles and responsibilities?
Does security training include how to communicate employee and management concerns regarding potential indicators of an insider threat?
Are practical exercises included in security awareness training that simulates actual cyberattacks?
DFARS Audit and Accountability
Does the company perform audit analysis and review?
Can the company uniquely trace and hold accountable users responsible for unauthorized actions?
Does the company review and update audited events annually or in the event of substantial system changes or as needed?
Configuration Management
Are baseline configurations developed, documented, and maintained for each information system type?
Are baseline configurations developed and approved in conjunction with the Chief Information Security Officer (CISO) or equivalent and the information system owner?
Are changes to the system authorized by company management and documented?
Identification and Authentication
Does the system make use of company-assigned accounts for unique access by individuals?
Are initial passwords randomly generated strings provided via a password reset mechanism to each employee?
Is multifactor authentication used for network access to privileged and non-privileged accounts?
Incident Response
Is there a company incident response policy that specifically outlines requirements for handling of incidents involving CUI?
Is there a company incident response policy that specifically outlines requirements for tracking and reporting incidents involving CUI to appropriate officials?
Does the company test its incident response capabilities for regular testing and reviews/improvements?
Maintenance
Are IT system maintenance tools (e.g., tools used for diagnostics, scanner and patching tools) managed?
Are controls in place that limit the tools, techniques, mechanisms, and employees used to maintain information systems, devices, and supporting systems?
Are all activities of maintenance personnel (who do not normally have access to a system) monitored?
Media Protection
Are documented workflow, data access controls, and media policy enforced to ensure proper access controls?
Is access to media from CUI systems provided only to approved individuals? Does the company only provide access to media from CUI systems to approved individuals?
Is system digital and non-digital media sanitized before disposal or release for reuse?
Personnel Security
Are individuals requiring access screened before access is granted?
Does the company revoke authentication/ credentials associated with the employee upon termination or transfer within a certain timeframe? (e.g., 24 hours)
Does the company retrieve all company information system-related property from the terminated or transferred employee within a certain timeframe? (e.g., 24 hours)
Physical Protection
Has the facility/building manager designated building areas as “sensitive” and designed physical security protections (including guards, locks, cameras, card readers, etc.) to limit physical access to the area to only authorized employees?
Has the facility/building manager reviewed the location and type of physical security in use (including guards, locks, card readers, etc.) and evaluated its suitability for the company’s needs?
Are all visitors to sensitive areas always escorted by an authorized employee?
Risk Assessment
Does the company have a risk management policy?
Are systems periodically scanned for common and new vulnerabilities?
Do system owners and company managers upon recognition of any vulnerability provide an action plan for remediation, acceptance, avoidance, or transference of the vulnerability risk?
Security Assessment
Has a periodic (e.g., annual) security assessment been conducted to ensure that security controls are implemented correctly and meet the security requirements?
Are deficiencies and weaknesses identified in security requirements assessments added to the action plan within a specified timeframe (e.g., 30 days) of the findings being reported?
Is there an assessor or assessment team to monitor the security requirement in the system on an ongoing basis?
System and Communications Protection
Does the system monitor and manage communications at the system boundary and at key internal boundaries within the system?
Are the company’s information security policies (including architectural design, software development, and system engineering principles) designed to promote information security?
Does the system prevent remote devices that have established connections (e.g., remote laptops) with the system from communicating outside that communications path with resources on uncontrolled/unauthorized networks?
System and Information Integrity
Are system flaws identified, reported, and corrected within company-defined time periods?
Does the system automatically update malicious code protection mechanisms?
Are internal security alerts, advisories, and directives generated?