What is a food fraud mitigation plan?
After conducting a food fraud vulnerability assessment, a good food fraud mitigation plan must be designed to address all factors identified during the evaluation. GFSI requires proper documentation of the food fraud mitigation plan which also varies depending on the type of business, as well as the products, risks, ingredients, and geographical occupancy. A food fraud mitigation plan should also address areas such as management processes, workplace culture and ethics, supplier management, and food distribution processes.
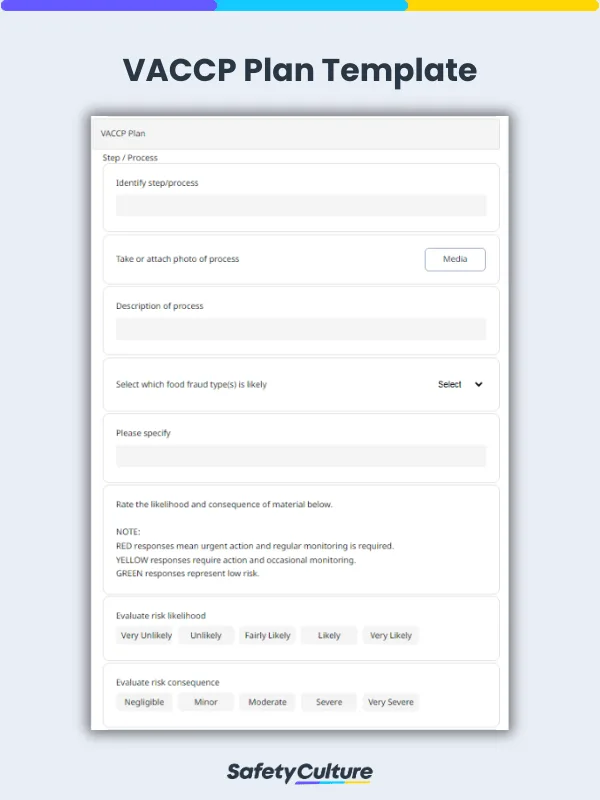
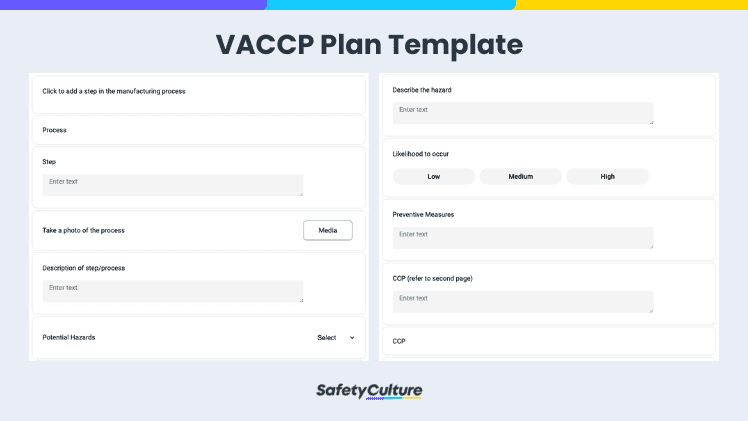
VACCP Plan | SafetyCulture
Is Food Fraud Illegal?
Food fraud is the deliberate “substitution, addition, tampering, or misrepresentation of food, food ingredients, or food packaging” for economic gain. While the consequences of food fraud may mostly go undetected by the human body, this does not nullify its harmful effects. Countless food fraud incidents over the last few decades prove how serious the threat it poses to public health. To prevent these incidents from recurring, food authorities globally have implemented various legal and certification requirements to hold food companies liable for the quality and safety of their products (e.g., FSMA, Regulation (EU) 2017/625). Non-compliance and violation of these food safety regulations and policies can lead to legal repercussions such as fines, suspensions, seizure and detainment of shipments, and worse closure.
Food Fraud Types
Here are some of the types of food fraud and example cases:
Counterfeiting – substitution of ingredients and products with similar packaging or the mixing of inferior quality ingredients to increase the volume of products, e.g. counterfeit spices (saffron, oregano, pepper) being mixed with different materials
Adulteration – adding ingredients like sugar or sweeteners to honey or maple syrup in order to produce a similar taste while adding volume or, in the case of baby formula, adding melamine to reach the desired “protein” count
Dilution – olive oil mixed with other types of oil, wine with grape blends, and fruit juices diluted in water then mixed with other ingredients to produce a similar taste while increasing volume
Mislabeling – examples are cases of horse meat mixed with beef but labeled and sold as beef, organic food being sold but found to have traces of “non-organic” ingredients, and mislabeled seafood being sold in the market
HACCP, TACCP, VACCP: What’s the Difference?
While there are control points among the three that overlap, the intention or goal is unique for each of them:
HACCP – stands for Hazard Analysis Critical Control Point and its goal is to identify and mitigate hazards during food production and ensure that the product is safe for consumption
TACCP – stands for Threat Assessment Critical Control Point and it aims to protect food products from deliberate contamination with the intention to cause harm
VACCP – seeks to identify and control vulnerabilities in the food supply chain that can be susceptible to food fraud
Food Fraud Vulnerability Assessment Example
It is highly recommended to monitor raw materials to prevent food fraud during the production process. One of the key areas for inspection is to check the quality of the raw food and its physical condition. Quality metrics should also be included to ensure that food will comply with industry standards. Here is an example of a food fraud vulnerability assessment for raw materials monitoring:
Food Fraud Vulnerability Assessment – Monitoring | SafetyCulture