What is GDPR?
GDPR (General Data Protection Regulation) is a data privacy and security law of the European Union that touches on the rights of individuals in controlling how their personal data is collected and processed by data organizations. GDPR aims to raise accountability for data protection by placing new obligations for organizations, allowing them to react faster and minimize potential damage from data breaches. This legislation applies to any firm operating within the EU and those holding EU citizen data regardless of their geographical location. Non-compliance with the GDPR can result in costly fines and penalties of up to €20 million ($22,263,100) or 4% of global revenue and can cause significant reputational damage.
3 Necessary Measures for Achieving GDPR Compliance
Compliance with GDPR falls into how organizations follow the regulation’s principles. Below are the 3 of the 7 principles under GDPR and its corresponding measures to mitigate exposure to regulatory penalties.
Accountability Accountability is a GDPR principle that focuses on organizations’ responsibility to comply with GDPR and to demonstrate compliance.
Implement data protection policies, organizational security measures, and data governance guidelines using data governance checklists
Document collected data, hence providing its use, its storage location, and the employee responsible for it
Have data protection or data processing agreement contracts with third party processors
Data Security This principle requires to handle data securely by implementing the “appropriate technical and organizational measures.”
Implement technical measures such as encryption, pseudonymization or anonymization of personal data
Implement organizational measures such as staff training and limiting access to personal data
Carry out data protection impact assessments
Have processes in place for data breaches (e.g., a system that notifies data subjects)
Lawfulness, fairness, and transparency This principle requires data to process personal data fairly. This obligates informing data subjects what and where their personal data will be used for.
Conduct information audits to determine the information process and people who have access to it. (e.g., impact assessments, comprehensive risk assessment, gap analysis)
Have a legal justification for data processing activities
Provide concise, transparent, intelligible and easily understandable information of data processing to inform users how and why you manage and use their data
These are just three out of several other more provisions of GDPR. Achieve full compliance by seeking legal advice from lawyers that specialize in GDPR to determine which provisions apply to your circumstances. Use GDPR compliance forms to ensure an accurate record of GDPR audits.
GDPR Compliance in the US vs EU
The GDPR (General Data Protection Regulation) originated in the European Union (EU) that applies to organizations worldwide that collect, store, or process personal data. Its scope extends beyond the EU borders, meaning that US companies can be subject to GDPR if they meet certain criteria. However, GDPR compliance in the US has a few differences.
GDPR Compliance in the EU
GDPR applies to all organizations operating within EU member states, as well as those outside the EU that offer goods or services to, or monitor the behavior of, EU residents.
Each EU member state has a Data Protection Authority (DPA) responsible for enforcement and handling complaints.
The GDPR includes rights such as the “right to be forgotten” and requires organizations to conduct impact assessments for sensitive data processing.
GDPR Compliance in the US
US companies are subject to GDPR if they have an establishment in the EU (e.g., branch, employee) or if they target or monitor EU residents for goods or services, regardless of where the processing occurs.
The GDPR does not apply to EU citizens physically located in the US; location takes precedence over citizenship.
US companies without EU assets must appoint an EU-based representative (Data Protection Officer) to liaise with EU regulators.
US federal and state agencies must comply with GDPR when processing EU residents’ data, with limited exceptions that do not apply to the US government.
Enforcement in the US is carried out by EU DPAs, which can impose fines and penalties; US companies with EU presence may face asset seizure for non-compliance.
Unlike the EU’s unified approach, the US has a fragmented data privacy landscape with state-level laws such as CCPA (California Consumer Privacy Act) and others, but no comprehensive federal GDPR equivalent
What to Include in a GDPR Compliance Checklist
A comprehensive GDPR compliance checklist should cover key areas that ensure lawful, transparent, and secure processing of personal data while respecting individuals’ rights:
Lawful Basis and Transparency – Identify and document the legal reason for processing personal data. Clearly inform individuals about how and why their data is used through transparent, easy-to-understand privacy notices.
Data Security – Protect personal data with appropriate technical and organizational measures like encryption and access controls to prevent unauthorized access or loss.
Accountability and Governance – Keep records of data processing activities, appoint a Data Protection Officer if needed, conduct impact assessments for risky processing, and ensure third parties comply with GDPR.
Privacy Rights – Enable individuals to exercise their rights (access, correction, deletion, portability, objection) promptly and provide clear instructions on how to do so.
Completion – Regularly update privacy policies, conduct audits to find gaps, maintain compliance documentation, and have a plan to detect and report data breaches within required timeframes.
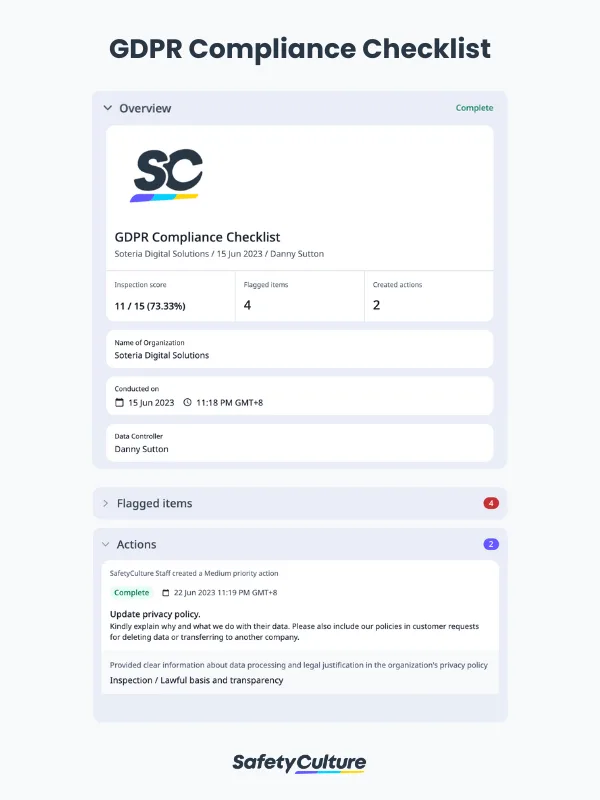
GDPR Compliance Checklist Sample Report | SafetyCulture