Strategies for Comprehensive Cybersecurity Risk Management
Learn about the key processes, tools, and best practices for managing cybersecurity risks and protecting an organization.

Learn about the key processes, tools, and best practices for managing cybersecurity risks and protecting an organization.

Published 7 May 2026
Article by
6 min read
Cybersecurity risk management is the systematic process of identifying, analyzing, and reducing risks related to data assets and digital systems. It involves rigorous assessment and the implementation of security controls to safeguard the privacy and reliability of all sensitive information and minimize operational vulnerabilities.
Cyber attacks have evolved into systemic threats that paralyze operations and erode public trust. While many understand how these can cripple industries, many companies are still unprepared to handle them. Here is why comprehensive cybersecurity risk assessment and risk management matters.
Safeguard sensitive data - Managing security isn't just about protecting the company’s business plans; it’s about looking out for the people they serve.
Protect financial stability - When a single security compromise costs over $10 million, companies should consider it a critical threat that can disrupt supply chains rather than just an IT issue.
Ensure business continuity - Any malicious intrusion can freeze production lines and halt services for weeks. Guarantee operational resilience through thorough system-wide checks and rigorous safety protocols.
Strengthen regulatory compliance - Strict regulations should not be considered as just additional paperwork. Look at these as vital safeguards that signal a commitment to digital integrity.
Enhance reputation and trust - Because trust is hard to build and easy to lose, companies must ensure that customer interests are safe. Cultivate cybersecurity safety by demonstrating that protective measures are just as reliable as the services provided.
Seamlessly identify and proactively mitigate risks to enhance organizational resilience and decision-making.
Cybersecurity risk assessmen t extends far beyond the IT department. It demands shared accountability, as a single lapse in judgment or a flawed process can create vulnerabilities that compromise the entire organization.
Executive leadership sets the tone by defining strategies, allocating funds, and prioritizing risk management.
IT and cybersecurity teams implement technical defenses and controls that enable them to quickly respond to incidents. They also maintain the system, ensuring it is protected against evolving threats.
Risk management and compliance teams identify, analyze, and monitor system threats. Closing security gaps is essential for maintaining compliance with regulatory standards and legal requirements.
Employees and end users are expected to adhere to security policies, use strong passwords, and recognize threatening activities (e.g., phishing, DDoS attack, ransomware). These core practices are the first line of defense for the entire operation
Build from scratch or choose from our collection of free, ready-to-download, and customizable templates.
Integrating cybersecurity risk management frameworks into the operations is a struggle for many organizations, even for large, global conglomerates. The path to a resilient defense is to understand the following risks well.
Evolving threat landscape - Defenses often become outdated because cyberthreats change. The inability to maintain up-to-date controls increases vulnerability and unexpected breaches.
Human error and insider risks - Accidental breaches and credential leaks are often caused by simple mistakes. Remember that uninformed employees ignore company policies, mishandle data, and easily fall for phishing scams.
Limited resources and budget constraints - Cybersecurity requires continuous investment. Many organizations that fall victim to attacks often lack sufficient funding, tools, or skilled personnel to maintain a proactive defense.
Complex IT environments - Complete oversight is hard to achieve across interconnected platforms and remote work environments. This leaves the operation more susceptible to threats.
Third-party and supply chain risks - The security practices of vendors and partners may be weaker because the company’s internal policies do not govern their operations. However, breaches on their end can jeopardize the entire operation.
Building a resilient security posture requires a structured approach, from the initial cybersecurity risk assessment process to diligent oversight of the implemented controls. Here’s a step-by-step guide on how this is done.
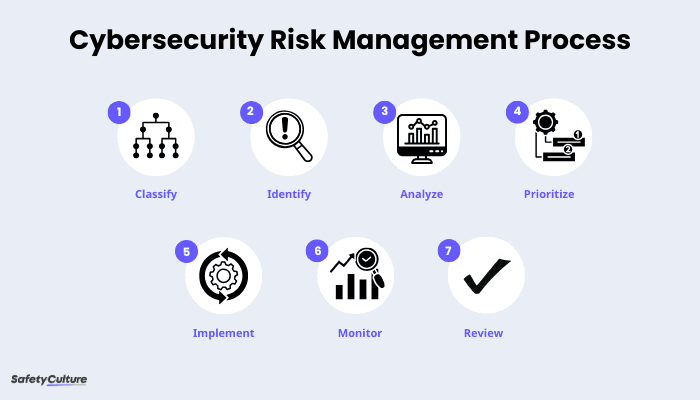
It is hard to secure something when the team does not know it exists. Start the cyber health check by listing systems, data, and digital resources that need protection. Here are some best practices to take note of:
Maintain an up-to-date asset inventory.
Classify data based on sensitivity (e.g., confidential, public, etc.)
Include cloud data, physical devices, and third-party assets.
Determine what could exploit the system and where weaknesses exist. Remember that threats can be external in nature or internal gaps. Here are some examples:
Phishing and social engineering
Malware and ransomware
Misconfigurations
Outdated software
Human error due to lack of training
Go through all cybersecurity risk assessment steps to comprehensively evaluate the likelihood and impact of the identified risks. Here’s a list of what to do and what tools and methods can help in the next phase.
Define the scope with asset management solutions and network discovery tools.
Identify threats through vulnerability scanners.
Check the likelihood of exploitation by using risk matrices and scoring models.
Assess potential impact with scenario or business impact analysis.
Calculate risk levels with scoring models from NIST
Use the assessment results to categorize risks by severity. Rather than attempting to mitigate every minor gap simultaneously, focus efforts on the most critical threats first to immediately reduce the company’s exposure.
This step transforms assessment into action. Reduce or eliminate risks by applying any of the following:
Preventive - firewalls, access controls
Detective - monitoring, intrusion detection
Corrective - patching, backups, incident response plans
Early detection reduces damage. This is achievable by continuously tracking systems and then responding to threats in real-time. Aside from establishing an incident response plan, invest in security monitoring tools to gain real-time visibility into emerging threats.
Tech is a fast-moving industry and constantly faces changes. Cybersecurity should be an ongoing process that requires regular evaluation and updates for strong mitigation against new and existing threats.
SafetyCulture is a mobile-first operations platform adopted across industries such as manufacturing, mining, construction, retail, and hospitality. It’s designed to equip leaders and working teams with the knowledge and tools to do their best work—to the safest and highest standard.
Maintain full visibility over interconnected assets, from cloud to physical systems, and standardize audits for speed and accuracy. Capture and resolve vulnerabilities instantly, then prevent recurrence by identifying root causes with advanced analytics. Educate workers to develop a strong proactive layer of defense. Empower teams to be in control of cybersecurity threats, ultimately achieving operational excellence, through a unified platform.
✓ Save and reduce costs
✓ Stay on top of risks and incidents
✓ Boost productivity and efficiency
✓ Enhance communication and collaboration
✓ Discover improvement opportunities
✓ Make data-driven business decisions
In this article