Cybersecurity Risk Assessment: The Ultimate Guide
Learn how structured cybersecurity risk evaluation helps organizations protect information, reduce vulnerabilities, and maintain resilient operations.

Learn how structured cybersecurity risk evaluation helps organizations protect information, reduce vulnerabilities, and maintain resilient operations.

Published 28 Apr 2026
Article by
6 min read
A cybersecurity risk assessment is a systematic process for identifying, analyzing, and evaluating potential threats and vulnerabilities that could negatively impact an organization's information systems.This process involves identifying the assets that need protection and evaluating the potential risks these assets face, including cyberattacks, data breaches, and system failures.
The assessment requires a comprehensive analysis of the likelihood and potential impact of these risks, allowing organizations to understand their security posture and prioritize remediation efforts.
In today's digital environment, conducting regular risk assessments is essential to strengthening cybersecurity and protecting organizational assets. With the global average cost of a data breach reaching USD 4.88 million, proactive vulnerability assessment has become a financial and operational necessity.
Here are some key reasons why vulnerability assessment is important for organizations:
Identifies security gaps early: Risk assessments uncover system vulnerabilities, misconfigurations, and control weaknesses before attackers can exploit them.
Reduces financial and operational impact: By proactively addressing risks, organizations minimize costly downtime, incident response expenses, and long-term recovery costs.
Protects reputation and customer trust: Preventing breaches helps maintain stakeholder confidence and avoids reputational damage that can follow public cyber incidents.
Ensures regulatory compliance: Proactive cybersecurity risk assessment supports alignment with regulatory frameworks such as ISO 27001, NIST, GDPR, HIPAA, and PCI DSS to reduce the likelihood of penalties or sanctions.
Strengthens cybersecurity resilience: Enhances preparedness by integrating risk management into security strategy, enabling faster detection, response, and recovery.
Supports business continuity planning: Identifies potential disruption points and helps organizations develop response and recovery plans to maintain operations during cyber incidents.
Cultivate a culture of excellence with our digital solutions that enhance efficiency, agility, and continuous improvement across all operations.
Organizations can address cyber risk through various frameworks and models tailored to their needs, regulatory requirements, and maturity levels. These frameworks help organizations systematically identify, assess, and manage cyber risks.
Some commonly used cybersecurity risk assessment frameworks include:
Qualitative assessments categorize cyber risks using descriptive scales such as low, medium, or high based on expert judgment. These models are commonly visualized through risk matrices or heat maps and are useful when precise data is unavailable.
Qualitative methods are often aligned with frameworks such as the NIST CSF to communicate risks across technical and executive teams. While they allow rapid evaluation across multiple systems, they rely heavily on assessor expertise and may lack consistency in audit or regulatory scenarios.
Quantitative approaches assign numerical values to cyber risks, often expressed in financial terms such as Annualized Loss Expectancy (ALE). These models require structured data on threat frequency, asset value, control effectiveness, and potential impact.
Frameworks such as NIST SP 800-30 support structured risk analysis, while methodologies like FAIR (Factor Analysis of Information Risk) and Monte Carlo simulations help calculate probable financial exposure. Quantitative assessments are particularly valuable when presenting cybersecurity investment decisions, insurance coverage, or risk tradeoffs to executive leadership.
Compliance-driven assessments align cybersecurity risk evaluations with regulatory and industry standards. Common standards include ISO/IEC 27001/27005, NIST SP 800-30, and sector-specific requirements such as PCI DSS or HIPAA.
These frameworks provide structured guidance for identifying control gaps and prioritizing remediation. While they align with regulations and standardize reporting, organizations must regularly evaluate control effectiveness alongside checklist compliance.
Build from scratch or choose from our collection of free, ready-to-download, and customizable templates.
Threat-informed models incorporate real-world adversary tactics, techniques, and procedures (TTPs) into cybersecurity risk analysis. By using threat intelligence and frameworks like MITRE ATT&CK, organizations prioritize risks based on active threat actors and industry-specific attack patterns.
This approach is particularly effective for critical infrastructure, financial institutions, and organizations operating in high-risk sectors. It strengthens resilience by aligning mitigation strategies with actual threat behavior rather than theoretical risk alone.
Modern cybersecurity environments evolve rapidly, making periodic assessments insufficient.
Continuous models use automation tools such as cloud security posture management (CSPM), cyber asset attack surface management (CAASM), and cloud-native application protection platforms (CNAPP) to provide near real-time risk visibility.
These tools integrate asset inventories, vulnerability data, control telemetry, and threat intelligence to generate dynamic risk scoring. Continuous assessment enhances operational accuracy and supports adaptive mitigation strategies in fast-changing digital environments.
Organizations should not treat cybersecurity risk assessments as one-time activities. Doing so is a core principle of cybersecurity risk management, which treats security as a continuous, evolving process rather than a box to check. Many experts recommend conducting internal reviews every six months or even quarterly.
Continuous risk assessment involves the following steps:
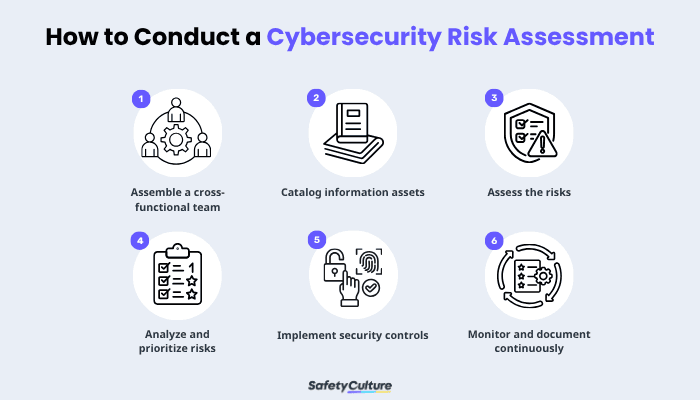
Begin by forming a team that includes IT, compliance, privacy, HR, product, and business leaders. A cross-functional approach ensures both technical and business risks are properly evaluated and aligned with broader cybersecurity governance objectives.
Identify all information assets including on-premise systems, cloud services (SaaS, PaaS, IaaS), networks, databases, and endpoints.
Document the types of data collected, where they are stored or transmitted, and who has access—including vendors and remote employees. Understanding authentication methods and system dependencies provides a clear picture of the organization's potential vulnerabilities.
Evaluate how the loss, compromise, or disruption of each asset would affect the business. Determine which systems and data are critical to confidentiality, integrity, and availability.
Consider potential financial, operational, and reputational consequences, and confirm whether business continuity and incident response plans are in place.
Score each identified based on probability and impact. Multiply these factors to determine overall risk levels and establish risk tolerance. Based on the results, decide whether to accept, avoid, transfer, or mitigate each risk.
Introduce controls to reduce the likelihood or impact of identified risks. These may include:
Network segmentation
Encryption (at rest and in transit)
Firewalls
Anti-malware tools
Multi-factor authentication
Strong password policies
Workforce training
Vendor risk management practices
Controls should directly address the highest-priority risks identified during analysis, as these pose the biggest risks that threaten operations.
Cyber risks evolve daily, making consistent monitoring essential. Use continuous control monitoring, real-time detection tools, penetration testing, and periodic audits to validate security posture. Maintain a detailed risk register to document findings, mitigation efforts, and residual risk, ensuring transparency and audit readiness over time.
SafetyCulture is a mobile-first operations platform adopted across industries such as manufacturing, mining, construction, retail, and hospitality. It’s designed to equip leaders and working teams with the knowledge and tools to do their best work—to the safest and highest standard.
Streamline processes, eliminate bottlenecks, enhance resource utilization, and build an agile and scalable infrastructure with SafetyCulture. Strive for operational excellence to boost competitive advantage, foster sustainable growth, and deliver long-term value.
Save time and reduce costs
Stay on top of risks and incidents
Boost productivity and efficiency
Enhance communication and collaboration
Discover improvement opportunities
Make data-driven business decisions