What Is an IT Security Audit?
An IT security audit is a systematic evaluation of an organization's information systems, controls, and processes against a defined security standard or framework. The goal is to identify gaps, verify that controls are operating as intended, and produce a risk-rated findings report that guides remediation.
Importance
A well-executed IT security audit should deliver:
A clear picture of which controls are in place, partially implemented, or missing entirely
Evidence packages mapped to your chosen framework (NIST, ISO 27001, SOC 2, PCI DSS, HIPAA, SOX)
A risk-rated findings report with severity, business impact, and remediation ownership
An actionable remediation plan with timelines and retest criteria
An executive summary suitable for leadership, the board, or external regulators
What Does an IT Security Audit Cover?
Scope definition is where most audits succeed or fail. Before any testing begins, you need a written scope statement that answers these questions:
Which systems are in scope? Servers, endpoints, network infrastructure, cloud environments (AWS, Azure, GCP), SaaS platforms, and OT/IoT devices where applicable.
Which data flows and business processes are covered? Map the data lifecycle — creation, storage, transmission, and disposal — for each in-scope system.
Which vendors and third parties are included? Any vendor with access to your data or systems should be evaluated, at minimum through a SIG questionnaire or review of their SOC 2 Type II report.
Which regulatory frameworks apply? NIST CSF, CIS Controls, ISO 27001, SOC 2, PCI DSS, HIPAA, and SOX each impose different control requirements. Define the
Types of IT Security Audits
Not every audit looks the same. The type you choose — or are required to conduct — depends on your regulatory environment, organizational size, and specific security risk concerns.
1. Information Security Audit
The broadest type. Covers technology, policies, procedures, and governance. Goes beyond systems to evaluate whether the organization's security program as a whole is effective. Typically maps to ISO 27001 or NIST CSF.
2. Cybersecurity Audit
Focuses specifically on cyber-threat controls: threat detection, incident response, vulnerability management, and resilience. Often used by organizations benchmarking against the NIST Cybersecurity Framework or CIS Controls.
3. Application Security Audit
Targets software — both internally developed and third-party applications. Includes code review (SAST/DAST), API security, authentication controls, and secure SDLC process verification.
Driven by a specific regulatory requirement: SOC 2, PCI DSS, HIPAA, SOX, or a US state breach notification law. The checklist is largely pre-defined by the standard; the audit verifies conformance.
5. Cloud Security Audit
Examines controls within cloud environments under the shared-responsibility model. Covers identity federation, storage bucket permissions, network security groups, logging configuration, and SaaS admin settings.
6. Enterprise Security Audit
A comprehensive, organization-wide audit that combines multiple types above. Typically performed by a third-party firm for large organizations with complex environments. May feed directly into a board-level risk report or external certification.
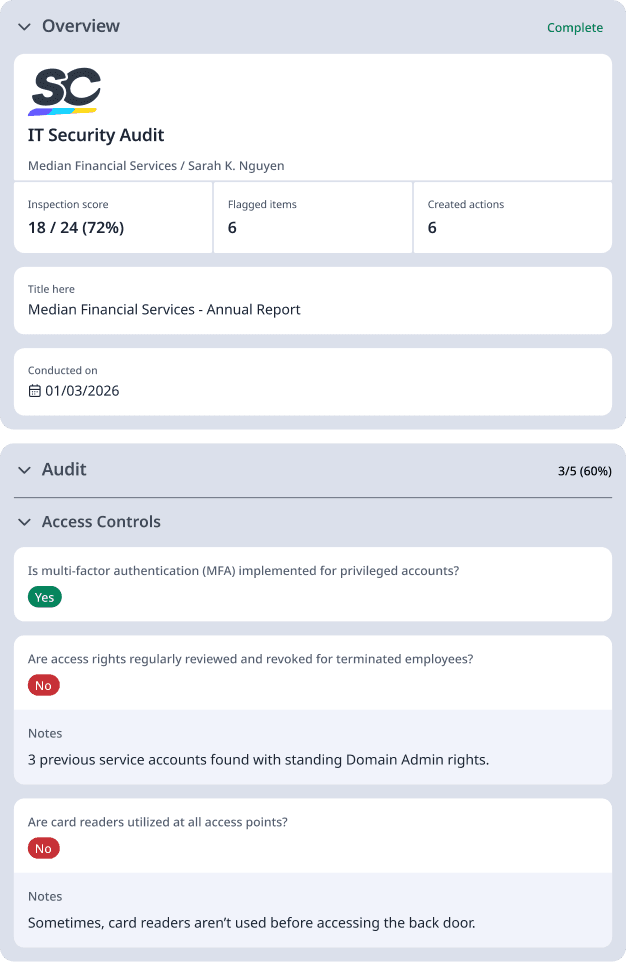
What to Include in an IT Security Audit Checklist
A practical IT security audit checklist is organized by control domain, includes a clear pass/fail criterion for each item, names the evidence required, and maps to at least one framework reference. Below is a condensed version of the key sections.
Pre-Audit Scoping — Defines the audit boundaries and ensures all groundwork is in place before fieldwork begins, including asset inventory, applicable frameworks, and stakeholder alignment.
Identity and Access Management — Reviews how user and system access is granted, monitored, and revoked to ensure only authorized individuals can reach sensitive resources.
Network Security — Evaluates firewall rules, network segmentation, remote access controls, and open ports to protect the organization's infrastructure from unauthorized access.
Patch and Vulnerability Management — Assesses how quickly known vulnerabilities are identified and remediated, and whether end-of-life systems are tracked and addressed.
Endpoint Protection — Confirms that all devices are covered by detection tools, encryption, and compliance policies to reduce the risk of compromise.
Data Protection — Verifies that sensitive data is properly classified, encrypted at rest and in transit, and monitored through data loss prevention controls.
Backup and Recovery — Checks that critical systems are backed up regularly, stored offsite, and that recovery has been successfully tested within the required timeframe.
Logging and Monitoring — Ensures security events are captured, retained, and actively reviewed, with a tested incident response plan in place.
Cloud and SaaS Controls — Examines access permissions, storage exposure, logging, and vendor security posture across cloud and third-party platforms.
How to Conduct an IT Security Audit
Here’s how to perform a foolproof IT security audit for your organization:
Phase 1: Pre-Audit Planning and Scoping
Define scope — document all in-scope systems, data flows, locations, vendors, and applicable frameworks.
Assign the RACI — name evidence owners for each control domain.
Select or build your checklist — use a framework-aligned checklist (see next section) and customize it for your environment.
Schedule kickoff — brief all stakeholders, explain evidence collection procedures, and set a timeline with milestones.
Gather baseline documentation — collect existing policies, previous audit reports, asset inventories, and network diagrams before testing begins.
Phase 2: Discovery and Evidence Collection
With scope confirmed, begin systematic discovery:
Asset discovery: Run network scans (e.g., Nmap, Qualys, Tenable) to enumerate live hosts, open ports, and running services. Cross-reference against your CMDB.
Configuration review: Pull configuration exports from firewalls, servers, Active Directory, and cloud consoles. Compare against CIS Benchmarks or vendor-recommended hardening guides.
Vulnerability scanning: Run authenticated scans across in-scope systems. Prioritize CVEs with CVSS scores of 7.0 or above.
Log and access reviews: Export user access lists (ACLs), privilege group memberships, and log samples from your SIEM. Verify MFA is enforced for all privileged accounts.
Interviews: Conduct structured interviews with IT operations, the security team, HR (for offboarding), and development (for change management and SDLC). Document responses.
Phase 3: Control Testing
Test each control against its defined pass/fail criteria:
Control | Acceptable Evidence |
MFA enabled for all admin accounts | Screenshot of IdP policy + user report showing 0 exceptions |
Patch SLA met (critical: 14 days) | Patch management report showing remediation dates vs. CVE disclosure dates |
Privileged access reviewed quarterly | Access review sign-off records with dates and reviewer names |
Firewall rules reviewed annually | Change tickets showing ruleset review + current ruleset export |
Logs retained for 12 months | SIEM retention policy configuration + sample log query confirming earliest entry |
Backups tested within last 90 days | Restore test record signed by IT manager |
Security awareness training completed | LMS completion report showing >95% staff completion rate |
Phase 4: Reporting and Remediation
Draft findings — for each gap, document: control reference, finding description, risk rating (Critical/High/Medium/Low), business impact, and recommended remediation action.
Validate with evidence owners — share draft findings with the responsible parties for factual accuracy before finalizing.
Produce the report — include an executive summary, full findings table, evidence inventory, and framework mapping appendix.
Issue the remediation plan — assign an owner, deadline, and retest date to every finding.
Retest — verify remediation for Critical and High findings within 30–60 days. Document retest results as a formal close-out.